aside chanel | side channel blinding attack aside chanel In computer security, a side-channel attack is any attack based on extra information that can be gathered because of the fundamental way a computer protocol or algorithm is implemented, rather than flaws in the design of the protocol or algorithm itself (e.g. flaws found in a cryptanalysis of a cryptographic . See more Select the “ Items ” tab at the bottom. Choose the AirTag you want to view history for. Tap on “ Find ” to see the AirTag’s current or last known location. Scroll down and tap “ See Location History. This will display a map with pins for all the AirTag’s detected locations.
0 · what does side channel attack mean
1 · side channel blinding attack
2 · side channel blinding
3 · side channel attacks 2017
4 · side channel attack wikipedia
5 · how does side channel attack work
6 · cache side channel attack
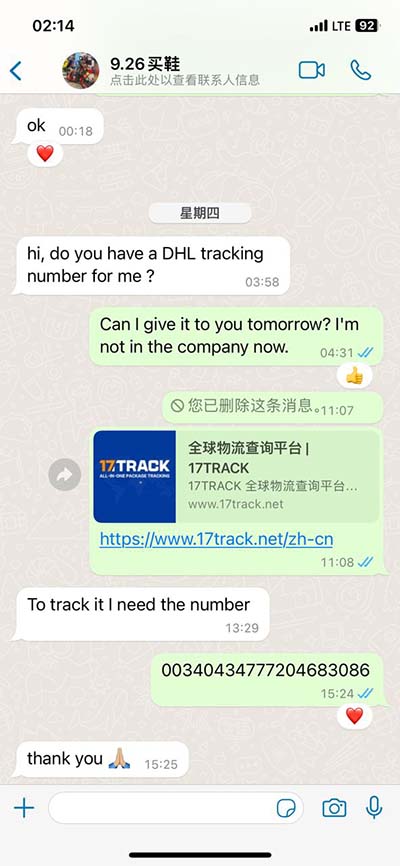
Contact: Our USA support centre can be reached on 1-866-668-4820 or 1-561-900-7160, between the hours of 8.00 AM to 7.00 PM (Eastern Time), Monday through Friday, and by e-mail. You can also contact our International Call Centre on Tel: +356 2166 2211.

In computer security, a side-channel attack is any attack based on extra information that can be gathered because of the fundamental way a computer protocol or algorithm is implemented, rather than flaws in the design of the protocol or algorithm itself (e.g. flaws found in a cryptanalysis of a cryptographic . See more
A cache side-channel attack works by monitoring security critical operations such as AES T-table entry or modular exponentiation or multiplication or memory accesses. The attacker then is able to recover the secret . See more• Brute-force attack• Computer and network surveillance• Covert channel• Side effect• Wire data See more
• Sima, Mihai; Brisson, André (2015), Whitenoise Encryption Implementation with Increased Robustness against Side-Channel Attacks• Brisson, André (2015),University of Victoria, British Columbia Side Channel Attack Resistance . See more
Because side-channel attacks rely on the relationship between information emitted (leaked) through a side channel and the secret data, . See moreBooks• Ambrose, Jude; et al. (2010). Power Analysis Side Channel Attacks: The Processor Design . See moreA.Side TV was a Canadian English language discretionary specialty channel owned by Blue Ant Media. Originally focusing on music and pop culture programming, the channel drifted towards generic true crime and paranormal programming before it wound down operations in mid-January 2023.In computer security, a side-channel attack is any attack based on extra information that can be gathered because of the fundamental way a computer protocol or algorithm is implemented, rather than flaws in the design of the protocol or algorithm itself (e.g. flaws found in a cryptanalysis of a cryptographic algorithm) or minor, but potentially .
A.Side TV was a Canadian English language discretionary specialty channel owned by Blue Ant Media. Originally focusing on music and pop culture programming, the channel drifted towards generic true crime and paranormal programming before it . Side-Channel Attack: A side-channel attack is a type of cybersecurity threat where the attacker gains information from the physical implementation of a computer system, rather than exploiting software vulnerabilities.
Computers constantly give off more information than you might realize—which hackers can use to pry out their secrets. Think of side channel attacks as the digital equivalent of a burglar.
what does side channel attack mean
side channel blinding attack
byu cheerleaders rolex
A side-channel attack is a type of security exploit that leverages unintended information leakage from a physical cryptosystem. Unlike traditional attacks that target the cryptographic algorithm itself, side-channel attacks focus on the implementation of the cryptosystem. What is a side-channel attack and how do they work? Side-channel attacks don't target cryptographic systems, but their implementations instead. Find out how they can compromise secure algorithms. Writer Josh Lake. Specialist in Security, Privacy and Encryption. Updated: August 4, 2023.A side-channel attack is a security exploit that aims to gather information from or influence the program execution of a system by measuring or exploiting indirect effects of the system or its hardware -- rather than targeting the program or its code directly.
A side-channel attack (SCA) is a security exploit that attempts to extract secrets from a chip or a system. This can be achieved by measuring or analyzing various physical parameters. Examples include supply current, execution time, and electromagnetic emission. Disable side channel mitigations for all virtual machines. After enabling WSL-2 under Windows 10 VMWare Workstation (Version 17.0.2 build-21581411) runs all virtual machines with side channel mitigations enabled. Even after disabling the features Hyper-V and WSL and restarting the system.source of information beyond the output speci ed by an abstraction is called a Side Channel. In this lecture, we will explore the history, examples, and countermeasures of side-channel attacks.
In computer security, a side-channel attack is any attack based on extra information that can be gathered because of the fundamental way a computer protocol or algorithm is implemented, rather than flaws in the design of the protocol or algorithm itself (e.g. flaws found in a cryptanalysis of a cryptographic algorithm) or minor, but potentially .A.Side TV was a Canadian English language discretionary specialty channel owned by Blue Ant Media. Originally focusing on music and pop culture programming, the channel drifted towards generic true crime and paranormal programming before it .
Side-Channel Attack: A side-channel attack is a type of cybersecurity threat where the attacker gains information from the physical implementation of a computer system, rather than exploiting software vulnerabilities.
Computers constantly give off more information than you might realize—which hackers can use to pry out their secrets. Think of side channel attacks as the digital equivalent of a burglar.A side-channel attack is a type of security exploit that leverages unintended information leakage from a physical cryptosystem. Unlike traditional attacks that target the cryptographic algorithm itself, side-channel attacks focus on the implementation of the cryptosystem. What is a side-channel attack and how do they work? Side-channel attacks don't target cryptographic systems, but their implementations instead. Find out how they can compromise secure algorithms. Writer Josh Lake. Specialist in Security, Privacy and Encryption. Updated: August 4, 2023.
A side-channel attack is a security exploit that aims to gather information from or influence the program execution of a system by measuring or exploiting indirect effects of the system or its hardware -- rather than targeting the program or its code directly. A side-channel attack (SCA) is a security exploit that attempts to extract secrets from a chip or a system. This can be achieved by measuring or analyzing various physical parameters. Examples include supply current, execution time, and electromagnetic emission. Disable side channel mitigations for all virtual machines. After enabling WSL-2 under Windows 10 VMWare Workstation (Version 17.0.2 build-21581411) runs all virtual machines with side channel mitigations enabled. Even after disabling the features Hyper-V and WSL and restarting the system.
brand positioning rolex
side channel blinding
We would like to inform you that Air Malta flights are currently operating out of London Heathrow Terminal 2. Please note that as from 22nd June 2022, Air Malta will recommence its operation from London Heathrow Terminal 4. Therefore flights will depart and arrive in this terminal.
aside chanel|side channel blinding attack